Cybersecurity has entered a new era. As businesses accelerate digital transformation, migrate to cloud platforms, adopt AI-driven systems, and enable remote workforces, the attack surface has expanded dramatically. In 2026, cyber threats are no longer isolated technical incidents—they are business-critical risks that can disrupt operations, damage brand reputation, and cause significant financial loss.
What makes cybersecurity especially challenging today is the speed and sophistication of modern attacks. Cybercriminals are using automation, artificial intelligence, and advanced social engineering techniques to exploit vulnerabilities faster than ever before. Traditional security models that rely only on perimeter defense or manual monitoring are no longer sufficient.
This blog explores the top cybersecurity threats businesses face in 2026 and outlines practical, modern strategies organizations can adopt to protect their digital assets, data, and operations.
Why Cybersecurity Is a Boardroom Priority in 2026
Cybersecurity is no longer just an IT concern—it is a strategic business issue. Data breaches, ransomware attacks, and system outages directly impact revenue, compliance, customer trust, and operational continuity.
Several factors have made cybersecurity more complex in 2026:
-
Increased reliance on cloud and hybrid infrastructures
-
Widespread adoption of AI and automation
-
Growth of remote and hybrid work environments
-
Rising volume of sensitive customer and business data
-
Tighter data protection and compliance regulations
As a result, organizations must shift from reactive security measures to proactive, intelligence-driven cybersecurity strategies.
Top Cybersecurity Threats Businesses Face in 2026
Understanding the threat landscape is the first step toward building effective defenses. Below are the most critical cybersecurity threats affecting enterprises today.
1. AI-Powered Cyber Attacks
Just as businesses are using AI to improve efficiency, cybercriminals are using AI to launch more targeted and scalable attacks. AI-powered malware can adapt in real time, evade detection, and exploit vulnerabilities faster than traditional attacks.
These attacks often involve automated phishing campaigns, intelligent malware that changes behavior, and advanced reconnaissance techniques that identify weak entry points in enterprise systems.
AI-driven threats significantly reduce the time organizations have to detect and respond, making traditional rule-based security tools less effective.
2. Ransomware and Double Extortion Attacks
Ransomware continues to be one of the most damaging cyber threats in 2026. Attackers no longer just encrypt data—they also steal sensitive information and threaten to leak it publicly if the ransom is not paid.
This “double extortion” approach puts immense pressure on organizations, especially those handling sensitive customer, financial, or government data.
Ransomware attacks can lead to prolonged downtime, regulatory penalties, and long-term reputational damage.
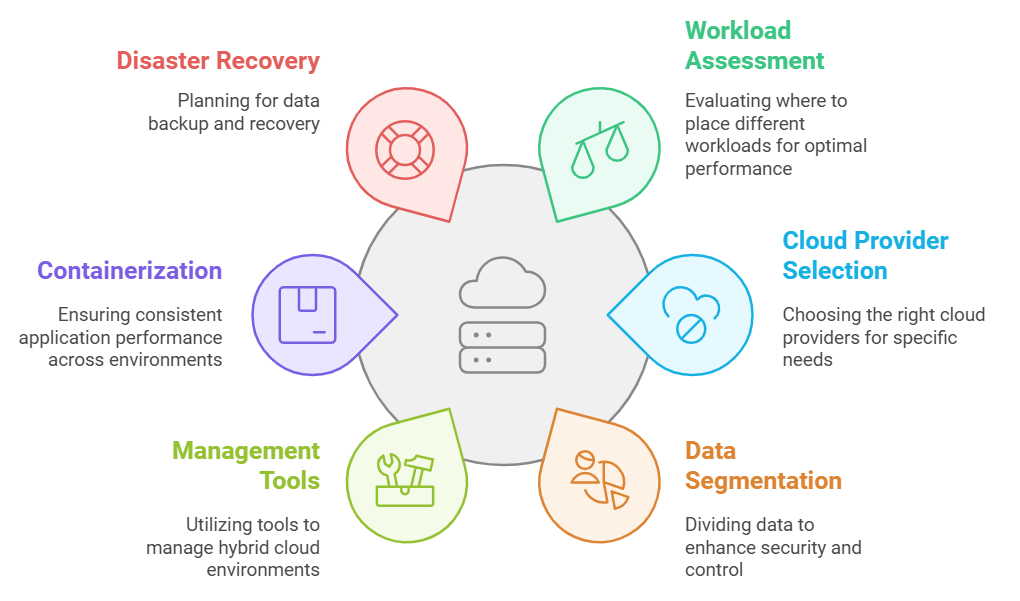
3. Cloud Security Vulnerabilities
As organizations move workloads to cloud and hybrid environments, misconfigurations and poor access controls have become major security risks. Many breaches occur not because of flaws in cloud platforms themselves, but due to improper implementation and monitoring.
Common cloud-related risks include exposed storage buckets, weak identity and access management, insecure APIs, and a lack of visibility across multi-cloud environments.
Without proper cloud security governance, businesses remain vulnerable despite using modern infrastructure.
4. Phishing and Social Engineering Attacks
Phishing remains one of the most effective attack vectors because it targets human behavior rather than technology. In 2026, phishing attacks are more convincing than ever, often using AI-generated emails, voice deepfakes, and impersonation techniques.
Attackers exploit trust by posing as executives, vendors, or trusted partners, tricking employees into revealing credentials or authorizing fraudulent transactions.
Even organizations with strong technical defenses can be compromised through a single successful phishing attempt.
5. Insider Threats
Not all threats come from outside the organization. Insider threats—whether malicious or accidental—continue to pose serious risks. Employees, contractors, or partners with legitimate access can unintentionally expose sensitive data or intentionally misuse it.
With remote work and third-party access becoming more common, monitoring user behavior and access privileges has become increasingly complex.
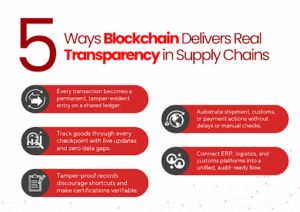
6. Supply Chain and Third-Party Attacks
Modern enterprises rely heavily on third-party vendors, software providers, and service partners. Cybercriminals often target these weaker links to gain access to larger organizations.
A single compromised vendor can expose multiple businesses to data breaches or system disruptions, making supply chain security a major concern in 2026.
How Businesses Can Protect Themselves in 2026
Defending against modern cyber threats requires a layered, proactive, and intelligence-driven approach. Below are key strategies organizations should implement.
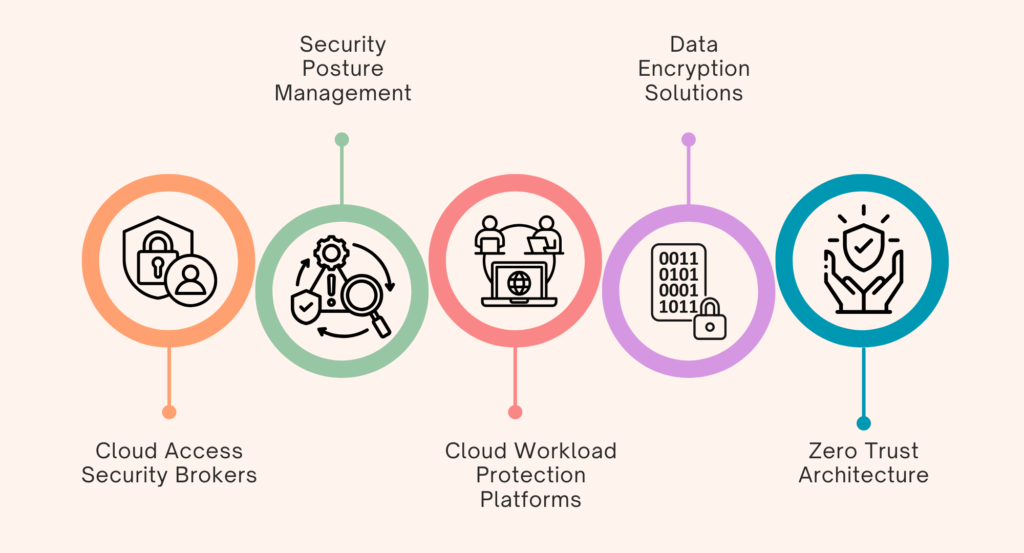
1. Adopt a Zero Trust Security Model
Zero Trust operates on the principle of “never trust, always verify.” Instead of assuming internal users or systems are safe, every access request is continuously validated.
This approach significantly reduces the risk of unauthorized access, lateral movement, and insider threats.
Zero Trust is especially critical for organizations with remote employees, cloud infrastructure, and third-party integrations.
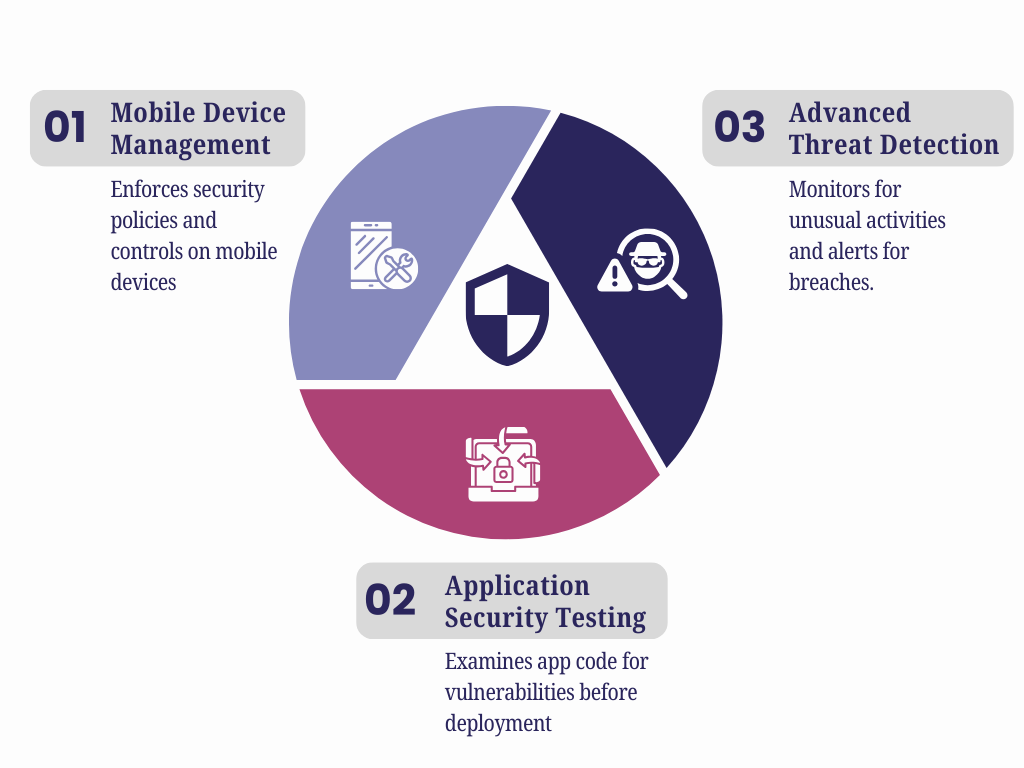
2. Use AI-Driven Threat Detection and Response
AI-powered security systems analyze massive volumes of data in real time to detect unusual behavior and potential threats. These systems can identify anomalies that human analysts or traditional tools might miss.
AI-based Security Operations Centers (SOCs) enable faster detection, automated response, and reduced false positives, allowing security teams to focus on high-risk incidents.
3. Strengthen Cloud Security Posture
Securing cloud environments requires more than basic firewalls. Organizations must implement strong identity and access management, continuous configuration monitoring, and encryption for data at rest and in transit.
Regular cloud security audits and real-time visibility across environments are essential to prevent misconfigurations and unauthorized access.
4. Invest in Employee Cybersecurity Awareness
Employees remain the first line of defense against cyber threats. Regular training helps staff recognize phishing attempts, social engineering tactics, and risky behaviors.
Cybersecurity awareness programs should be ongoing, practical, and tailored to real-world attack scenarios rather than generic guidelines.
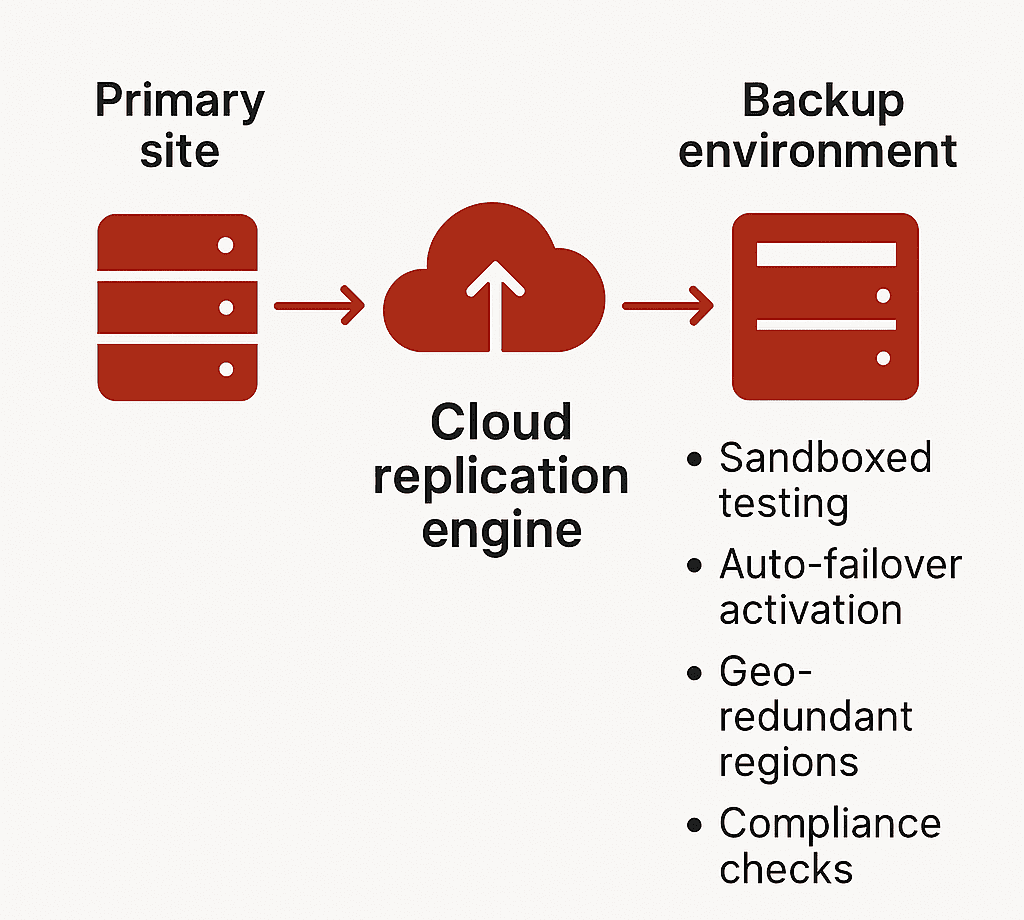
5. Implement Strong Data Protection and Backup Strategies
Data encryption, regular backups, and secure recovery mechanisms are essential for minimizing damage during cyber incidents. Backups should be isolated from primary systems to prevent ransomware from encrypting them as well.
A strong data protection strategy ensures business continuity even during major attacks.
6. Secure the Supply Chain
Organizations must assess the cybersecurity posture of vendors and partners. This includes regular risk assessments, contractual security requirements, and continuous monitoring of third-party access.
Supply chain security is no longer optional—it is a critical component of enterprise risk management.
7. Develop and Test Incident Response Plans
No system is completely immune to attacks. Having a well-documented and regularly tested incident response plan ensures organizations can act quickly and minimize damage when breaches occur.
Clear roles, communication protocols, and recovery procedures help reduce downtime and confusion during incidents.
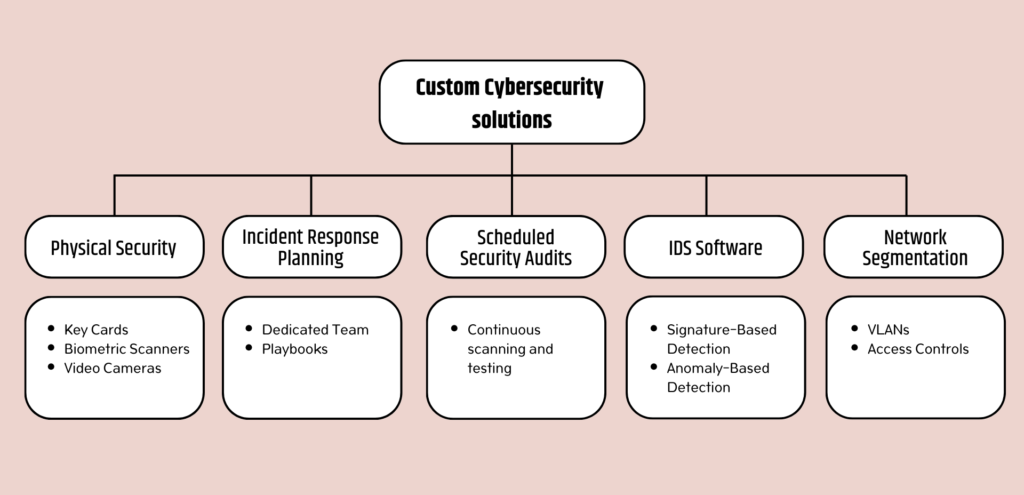
The Role of Strategic Cybersecurity Partners
Building robust cybersecurity capabilities in-house can be complex and resource-intensive. This is where experienced technology partners play a vital role.
SCS Tech India helps organizations strengthen their cybersecurity posture through end-to-end solutions that combine strategy, technology, and execution.
With expertise in cybersecurity consulting, cloud security, managed SOC services, and compliance-driven security frameworks, SCS Tech India enables businesses to move from reactive defense to proactive cyber resilience.
Wrapping Up!
Cybersecurity in 2026 is defined by complexity, speed, and intelligence—both on the attacker’s side and the defender’s. Businesses that rely on outdated security models are increasingly vulnerable to sophisticated threats that can cause severe operational and financial damage.
To stay secure, organizations must adopt modern cybersecurity strategies that combine AI-driven detection, Zero Trust principles, strong cloud security, employee awareness, and continuous monitoring.
Cybersecurity is no longer about preventing every attack—it’s about detecting threats early, responding quickly, and recovering effectively. With the right strategy and the right partners, businesses can protect their digital future and build long-term resilience in an increasingly connected world.