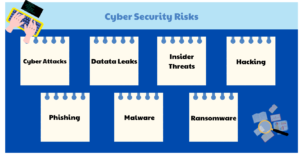
With the threat of cyberattacks looming larger than ever, if you think that your small and medium-sized businesses are safe, think again. Alarmingly, a recent report published by The CyberPeace Foundation stated that approximately 43% of data breaches occurred in small businesses and startups. With cybercriminals increasingly targeting smaller businesses, SMEs must recognize the critical importance of fortifying their defenses.
In this blog, we explore essential strategies to help SMEs thrive in an ever-evolving digital landscape.
Essential Cybersecurity Practices Every SMEs Must Implement
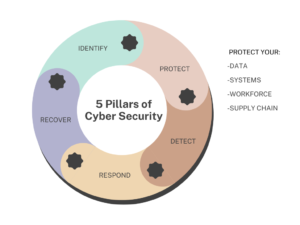
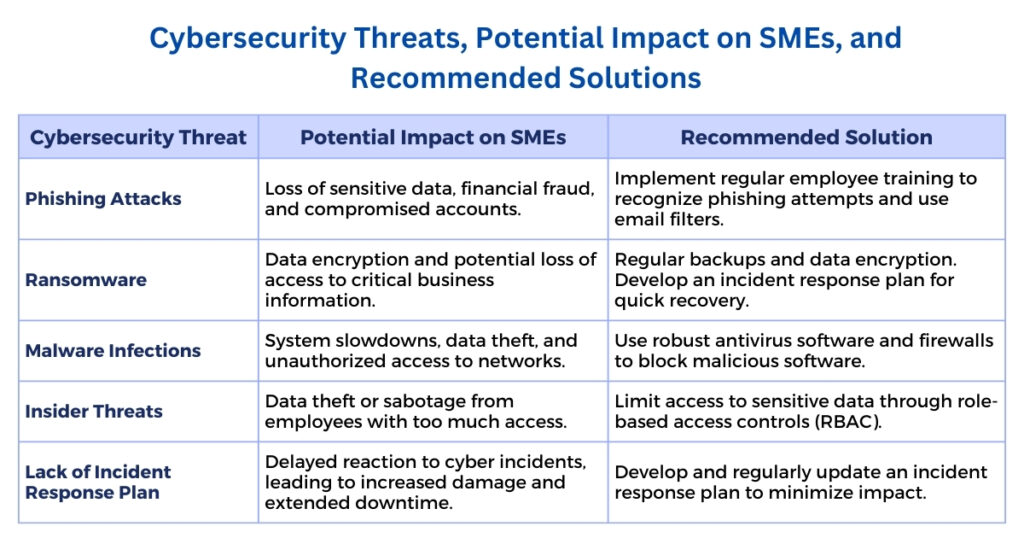
SMEs must focus on building their Cybersecurity Service walls, as they are vulnerable to cyberattacks due to their limited resources. Let us discuss the various practices that small and medium enterprises must implement as security measures to safeguard their sensitive data and mitigate risks:
- Updated Systems and Software: Managing updates of systems and software on a timely basis ensures the elimination of any security breaches, which further mitigates any chance of exploitation by attackers. It also promotes enhanced performance and compliance with all standards to eliminate any possibility of security compromises.
- Limit Access to Sensitive Data: This practice gives role-based data access control, which helps safeguard data against unauthorized activities and potential threats. This further enhances data safety and privacy.
- Secure Wi-Fi Networks: Transmission of sensitive data over wi-fi networks should be performed with complete security. This practice plays a crucial role in shielding data and maintaining network integrity. By using methods like strong encryption, timely updating of default settings, and solid passwords, we can substantially mitigate the risk of unwanted access and data breaches.
- Data Encryption and Regular Backups: Systematic backups of data regularly ensure protection against loss of data in case of any cyberattacks. On the other hand, implementation methods of strong encryption safeguard data against any unauthorized access, even if it is stolen or intercepted.
- Strong Password Policies and Multi-Factor Authentication: A solid password combined with multi-factor authentication (MFA), which involves more than one verification method to obtain access, guarantees an additional layer of security, which prevents any unauthorized access data in case of compromised passwords.
- Performing Regular Risk Assessments: Supervising regular risk assessments promotes the identification and management of potential pitfalls and susceptibilities. It also helps businesses to have an edge over evolving threats, assuring that the security needs are synchronized with the present risk environment and business demands.
- Firewalls and Antivirus Software: The implementation of proper firewalls acts as a shield between established internal networks and suspicious external networks and potential malware threats. On the other hand, antivirus software locates, defends, and eliminates any malicious content from systems and software.
- Employee Training on Cybersecurity Awareness: Organizations must focus on building a security-conscious environment that educates employees to recognize and respond to cyber threats because they are the first line of defense. By cultivating an environment of shared responsibility amongst the employees for cybersecurity service, SMEs can remarkably refine their safeguards against advancing cyber risks.
- Engaging with Third-Party Vendors: Working with trusted third-party vendors promotes the protection of sensitive data and reduces potential cyber risks through third-party systems. Organizations must ensure that these vendors work with stringent security protocols to prevent any data or security breaches.
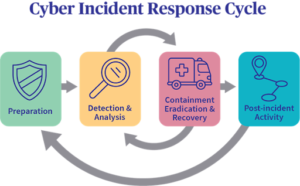
- Build an Incident Response Plan: Creating an effective incident response plan is extremely crucial for handling cybersecurity breaches or attacks. It is a standardized approach that ensures quick and adequate response to cyber threats by organizations while mitigating potential risks, reducing recovery time, and eliminating future cyber attacks. It also prevents any reputational damage by focusing on timely compliance with necessary protocols, which further builds customer trust.
Emerging Cybersecurity Trends and Technologies for SMEs
Emerging cybersecurity trends and technologies have started to pave the way for small and medium enterprises to engage in innovative methods to protect themselves from potential cyber risks. Let us explore these latest trends that SMEs should deploy to strengthen their cybersecurity structure:
#1 Artificial Intelligence (AI) and Machine Learning (ML) in cybersecurity
AI and ML services offer transformative benefits to SMEs by scrutinizing vast sets of data in no time while simultaneously analyzing the data for any security threats and early warnings.
#2 Endpoint detection and response (EDR)
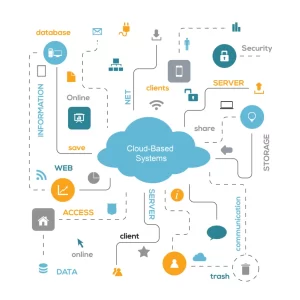
With the rising demand for remote work, protection of endpoints ( laptops, mobiles, etc.) has become extremely important. EDR focuses on finding and scrutinizing any malicious activities on these endpoints and isolating the same to prevent further damage.
#3 Zero Trust Architecture
With hybrid work environments in trend, conventional defenses are not enough to strengthen the cybersecurity of SMEs. Zero trust engages the concept of not trusting anybody in the internal or external networks.
#4 Security automation and orchestration (SOAR)
SOAR is a boon for organizations with a finite IT staff as it uses automation of repetitive tasks which helps in detecting, evaluating, and responding to cyber threats by amalgamating different security tools.
#5 Phishing awareness and training programs
SMEs employees often lack the training and knowledge to adequately fight against phishing and other cyber attacks. Building awareness against phishing attacks can enhance employee retaliation to real threats.
Conclusion
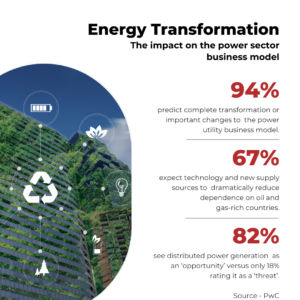
As cyber threats continue to rise, SMEs can no longer afford to remain complacent—especially with 46% of SMEs in India unaware of how to mitigate these risks. To safeguard sensitive and operational data while preserving customer trust, it’s crucial for organizations to adopt robust cybersecurity practices.
Collaborating with custom cybersecurity solutions providers like SCS Tech can enhance protection by integrating advanced technology into their systems while promoting business growth and minimizing risks.
FAQs
- Do SMEs have the resources to implement solid cybersecurity protocols?
Yes, SMEs can implement strong, cost-effective, and flexible cybersecurity measures with limited resources.
- How does the principle of least privilege work in SMEs?
The principle of least privilege involves allowing the user with minimum access rights to do their jobs to mitigate insider attacks and threats.
- In what ways can SMEs protect their staff against phishing attacks?
SMEs must ensure that employees have the knowledge to recognize suspicious emails, use spam filters, and encourage employees to report any phishing attempts.



 Various solutions for protecting digital assets with the help of custom cybersecurity
Various solutions for protecting digital assets with the help of custom cybersecurity