Just 39 seconds—that’s all it takes for a cyberattack to strike, faster than you can reply to your emails.
This alarming frequency indicates the urgent need for cybersecurity solutions. With every company relying on cloud computing, mobile devices, and on-site infrastructure, the demand for robust protection has never been greater. While each environment has its own unique vulnerabilities, cyber security consulting services help organizations identify and address these gaps effectively. General security measures may cover major threats, but expert consulting ensures even the less obvious vulnerabilities are not overlooked.
That is where custom cybersecurity solutions come in for each system, which are different, specified according to their needs, and used to counter specific threats.
Let’s discuss, in detail, each of the challenges presented by cloud, mobile, and on-site systems. Understand how custom cybersecurity solutions overcome those challenges, and improve security in each.
Security of Cloud Systems: Overcoming Unique Security Challenges
With the advent of cloud computing, tremendous flexibility and scalability emerged for businesses, but they differ through unique risks. With various users sharing cloud environments and being managed by third parties, they pose unique security issues that vary from traditional systems.
What Are the Challenges in Cloud Security?
- Data Breach: When sensitive information is stored in the cloud, it is most vulnerable to unauthorized access, especially if it has weak credentials or is not configured correctly.
- Account Hijacking: Compromise from phishing leads to allowing attackers access to valuable information.
- Insecure API: An insecure API control can be equated to an open door for an attacker with services in the cloud.
- Compliance Complexities: These are the complexities of the compliance cloud configurations that must be put into strict regulatory standards like GDPR or HIPAA. This is challenging to implement effectively.
How Do Custom Cybersecurity Solutions Enhance Cloud Security?
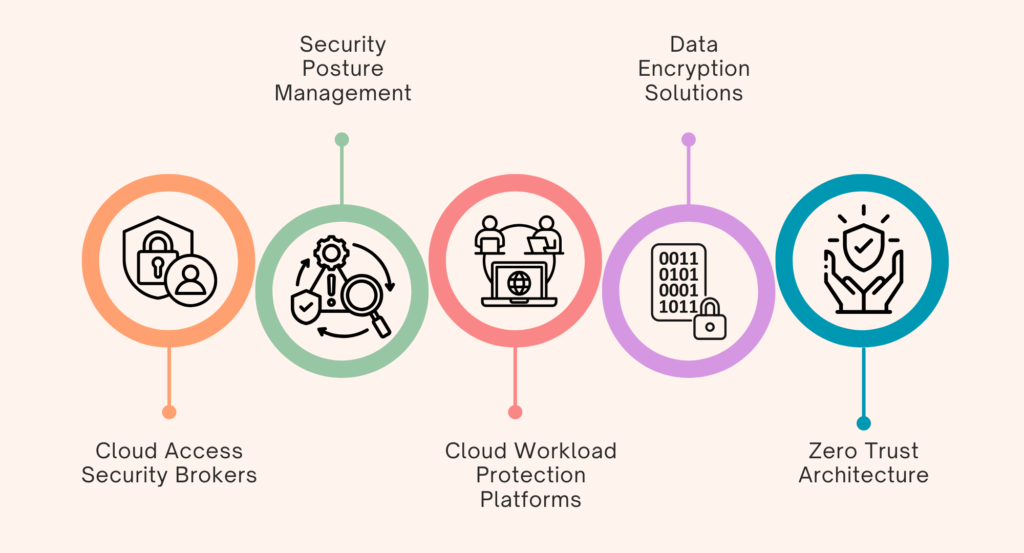
- Cloud Access Security Brokers (CASBs): CASBs serve as security layers between the cloud provider and the user base. It provides
- Data Protection: CASBs enforce data-loss-prevention policies through enforcing DLP policies by monitoring how data is transferred and blocking unauthorized access to sensitive information.
- Threat Detection: They use behavioral analytics to detect anomalies in user behavior that might suggest a breach.
- Compliance Management: CASBs help keep organizations compliant with all the appropriate industry regulations based on audit trails and reporting.
- Security Posture Management (SPM): SPM tools continuously watch for identifying vulnerabilities and misconfigurations in the cloud environments. This is done through:
- Vulnerability Scanning: Scanner tools that scan for all misconfigurations and known vulnerabilities in cloud resources.
- Compliance Audits: Periodic audits that the configurations adhere to best security practices and the appropriate regulations from the mandate.
- Cloud Workload Protection Platforms (CWPP): They protect the applications running in the cloud by analyzing activity in real-time and blocking unauthorized access attempts.
- Runtime Protection: The CWPP can detect real-time threats by protecting applications against malicious activity.
- Intrusion Prevention: The CWPP prevents any unauthorized access attempt and reduces the attack’s impact on workloads.
- Data Encryption Solutions: Encryption at rest, associated with the storage of data, and in motion, associated with the transfer of data utilise strong algorithms such as Advanced Encryption Standard (AES) coupled with Rivest-Shamir-Adleman (RSA) ensuring the integrity of data as it flows through all its stages of the life cycle.
- Encryption at Rest: With strong encryption algorithms such as AES-256, data is encrypted to secure those at rest in the cloud.
- Encryption in Transit: Encryption protocols, such as TLS/SSL, consist of specific ones that encrypt data between users and cloud services.
- Zero Trust Architecture: Zero Trust continuously verifies users and devices, limits network access, and controls lateral movement. This architectural model is designed so that not a single user or device should be trusted by default, regardless of whether they are inside or outside the network perimeter.
-
- Identity Verification: MFA ensures only the proper users can access cloud resources.
- Micro-Segmentation: This involves limiting lateral movement as the workload is segmented so multiple attack vectors remain inaccessible to the hackers if one resource is compromised.
Mobile Systems: Unique Risks and Custom Solutions for Security
The increasing use of mobile devices in the workplace has become a meaningful way to access company information. Still, they also pose vulnerabilities due to their portability and high connectivity. Among mobile security threats are malware attacks, phishing scams, and accidental data leaks in cases where information is mishandled.
What Are the Issues in Mobile Security?
- Threats of Malware: The mobile phone is highly vulnerable to malware that can steal away information or compromise system operations.
- Phishing Attacks: Mobile phishing attacks target mobile users with fake messages that compel the victims to unveil sensitive information.
- Leakage of Data: The leakage of data is facilitated by mishandling and storing some applications without appropriate security, thereby making them vulnerable.
How Do Custom Cybersecurity Solutions Improve Mobile Security?
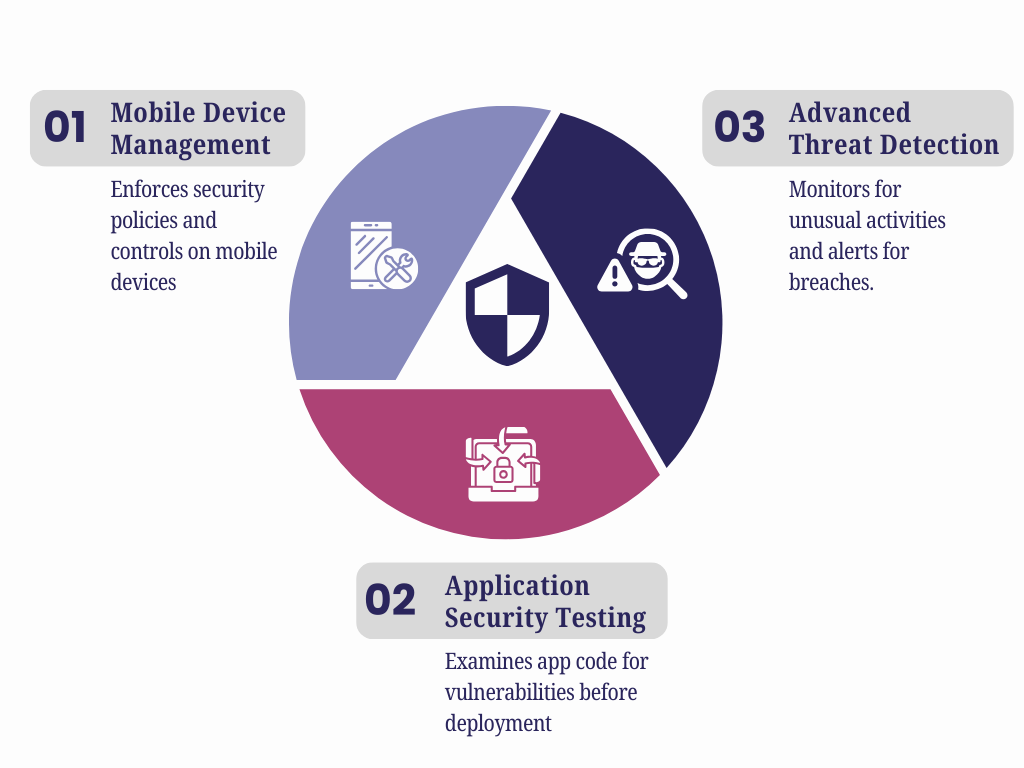
- Mobile Device Management (MDM): MDM will help enforce security policies across mobile devices and controls preventing the installation of unauthorized applications. This is done by:
- Wipe Remotely Ability: IT administrators can remotely wipe the data off lost or stolen devices so sensitive information cannot be accessed.
- Application Control: MDM enables organizations to mark applications as white lists or black lists depending on security policies to prevent malicious applications from being installed.
- Application Security Testing: This examines the code of a mobile application for potential vulnerabilities while simulating attacks to determine hidden weaknesses before deploying the app.
- Static Application Security Testing (SAST): It scans for possible weaknesses in the source code that may occur when executed.
- Dynamic Application Security Testing (DAST): Running applications are tested for vulnerability through simulated attacks that could reveal the exploits.
- Advanced Threat Detection: Behavioral analytics monitor mobile devices for unusual activities and enable an immediate response to potential breaches.
-
- Behavioral Analytics: These systems monitor patterns in the user behavior that signify a potential compromise.
- Real-Time Alerts: Instant alerting of suspicious events to allow for prompt investigation and action.
On-Site Systems: Controlling Internal and Physical Threats through Custom Cybersecurity Solutions
As businesses continue their digital transformation, on-site systems form the backbone of most organizations, since they provide a direct source of access to data coupled with control.
They are always vulnerable to internal threats and intrusion by physical persons. Insiders and unauthorized physical intrusion are the main risks to on-site systems.
What Are the Security Problems in On-Site Systems?
- Insider Threat: The insiders compromised the security since those authorized to privilege access may misuse their rights.
- Physical Violations: Unauthorized physical entities entering critical areas directly result in hardware or data exposure.
How Do Custom Cybersecurity Solutions Improve On-Site Security?
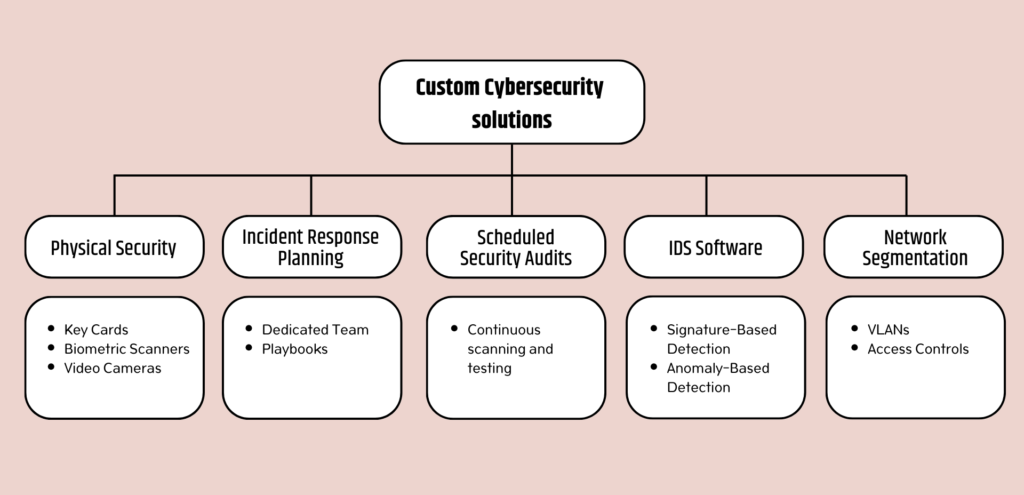
- Network Segmentation: Division of the network into sub-divisions. Segmentation limits the movement of attackers and restricts access to sensitive data. This format helps isolate breaches, thus protecting the rest of the network.
- Virtual Local Area Networks (VLANs): Separation of the different network-level departments reduces the likelihood of lateral movement by an attacker.
- Access Controls Between Segments: Strict access controls make sure that only authorized persons gain access to the sensitive segments.
- IDS Software: Intrusion Detection Systems (IDS) software keeps track of network traffic by detecting signatures and anomalies, which will notify of a threat in real-time.
- Signature-Based Detection: Predefined signatures of known threats are recognized and provide immediate responses to familiar attacks.
- Anomaly-Based Detection: This form of detection involves scanning for patterns that don’t fall under the usual traffic profile within the network. The method finds new threats that do not match existing signatures.
- Scheduled Security Audit: Periodic scanning for weaknesses and penetration testing will discover and remove all the possible vulnerabilities within the system before hackers take advantage of them.
- Incident Response Planning: A dedicated incident response team and a few playbooks for common scenarios ensure that breaches are fast and efficient and the eventual damage is reduced.
- Physical Security: Restrict access to building parts using key cards, biometric scanners, and video cameras.
Conclusion
Present-day generic solutions fail when unique challenges exist in cloud, mobile, and on-site systems. SCS Tech, a trusted name among the cybersecurity solutions group, provides targeted protection needed to keep data and operations safe.
Whether planning a new security strategy or seeking to build upon and enhance the existing one, investing in custom cybersecurity solutions is paramount in these times of constant global changes and cyber threats.