Ever feel like your teams are working hard, but projects still drag on? Delays, repeated approvals, and miscommunication can quietly eat away at productivity. The culprit is often operational bottlenecks, those invisible slow points that hold your entire workflow back.
The good news? With the right custom software, you can target these bottlenecks head-on, streamline operations, and help every department move faster and smarter.
What Are Operational Bottlenecks and Why They Happen
Operational bottlenecks happen when one step in a process slows down the entire workflow. Think of it like a traffic jam inside your company: one department gets stuck, and everything else piles up behind it.
Common causes include:
- Manual approvals – Tasks like expense approvals or HR requests can take days instead of hours.
- Disconnected systems – When your CRM, ERP, and project management tools don’t talk to each other, duplicate effort and errors pile up.
- Poor communication – Delayed updates or unclear responsibilities leave teams waiting on answers.
- Repetitive tasks – Time-consuming manual work steals focus from higher-value activities.
For example, a finance team manually reconciling invoices across multiple platforms might spend 10+ hours a week on a task that could be automated in minutes. Identifying these bottlenecks is the first step to freeing up time, reducing errors, and keeping your operations moving smoothly.
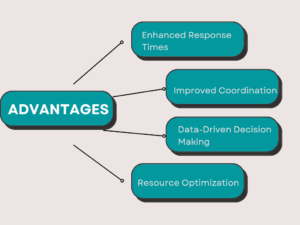
How Custom Software Targets Bottlenecks Across Departments

Custom software isn’t just about replacing old tools, it’s about making your workflows smarter, faster, and more connected. By tailoring solutions to your company’s unique processes, you can tackle bottlenecks at their source, so every department works more efficiently and teams spend less time chasing approvals or fixing errors.
Streamlining Communication
Think about your workflow as a chain: it’s only as fast as the slowest link. In many organizations, that link is communication. Delayed approvals, missed messages, or unclear responsibilities create a multiplier effect, one small delay can ripple across teams, slowing multiple projects at once.
Custom software addresses this by:
- Automating notifications and reminders – Industry research shows automation of routine business processes can reduce operational delays by up to ~40%, cutting much of the waiting time caused by manual handoffs
- Centralized dashboards – Instead of searching across emails, files, or chat apps, teams see the status of tasks at a glance. This follows the information visibility model, where quicker access to key data directly speeds decision-making.
- Integrated collaboration tools – Chat, comments, and task assignments in one place reduce time lost to context-switching; studies show knowledge workers spend roughly 2.5 hours per day searching for information or recovering from interruptions, and interruptions typically require ~20–25 minutes to fully refocus on a task.
For example, approvals that normally take 3 days can be reduced to a few hours. By removing friction from communication, teams can focus on execution instead of coordination, drastically reducing bottlenecks that often stall operations without anyone realizing it.
Automating Repetitive Tasks
Repetitive tasks are productivity killers. When teams spend hours on manual work, like entering data, reconciling spreadsheets, or generating reports, it’s not just time lost; it’s opportunity cost. According to the Pareto principle, roughly 20% of tasks generate 80% of value, meaning most repetitive work contributes little to strategic outcomes.
Custom software reduces these bottlenecks by:
- Automating manual processes – HR approvals, invoice processing, or inventory updates can be executed automatically, freeing your team to focus on high-value work.
- Reducing human error – Manual repetition increases the likelihood of mistakes, which can ripple downstream and cause rework. Automation follows the error reduction mental model, where reliability increases exponentially when routine tasks are systematized.
- Tracking workflows in real time – Software ensures every step is logged, measurable, and traceable, making it easier to spot and fix inefficiencies.
For instance, finance teams spending 10 hours a week reconciling data across platforms could cut that time to under an hour with automation. Across HR, operations, and administration, automating repetitive tasks not only accelerates processes but also boosts accuracy and employee satisfaction, turning bottlenecks into streamlined workflows.
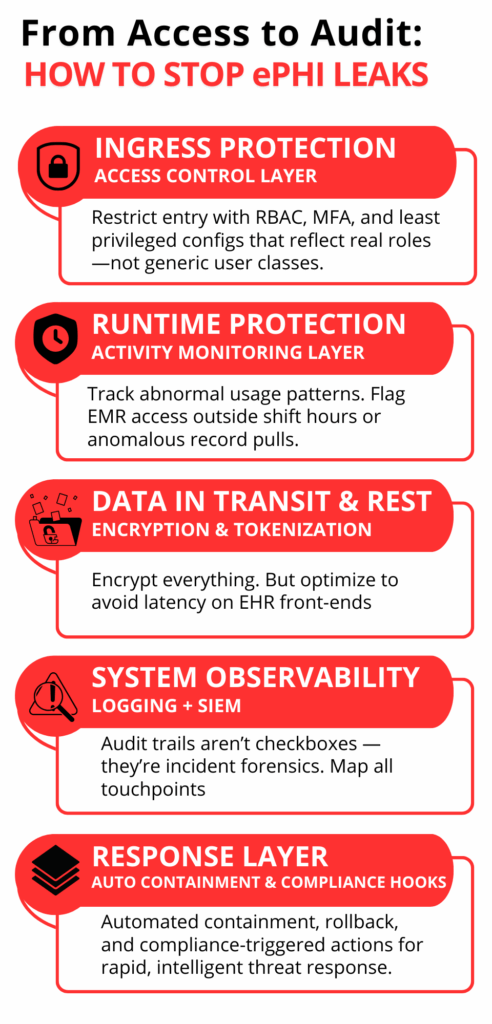
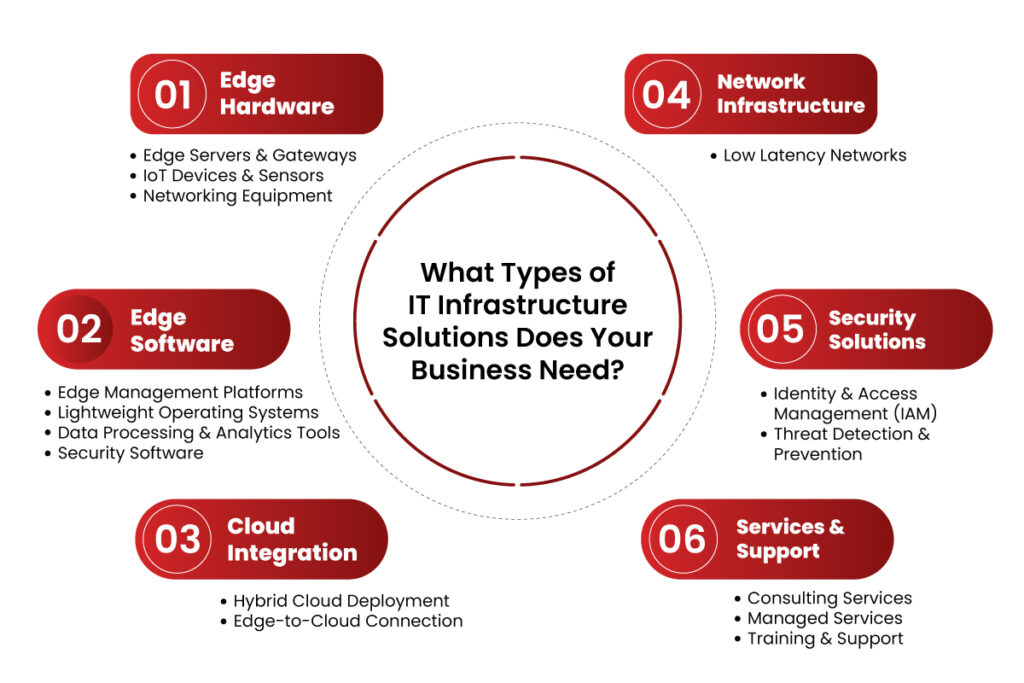
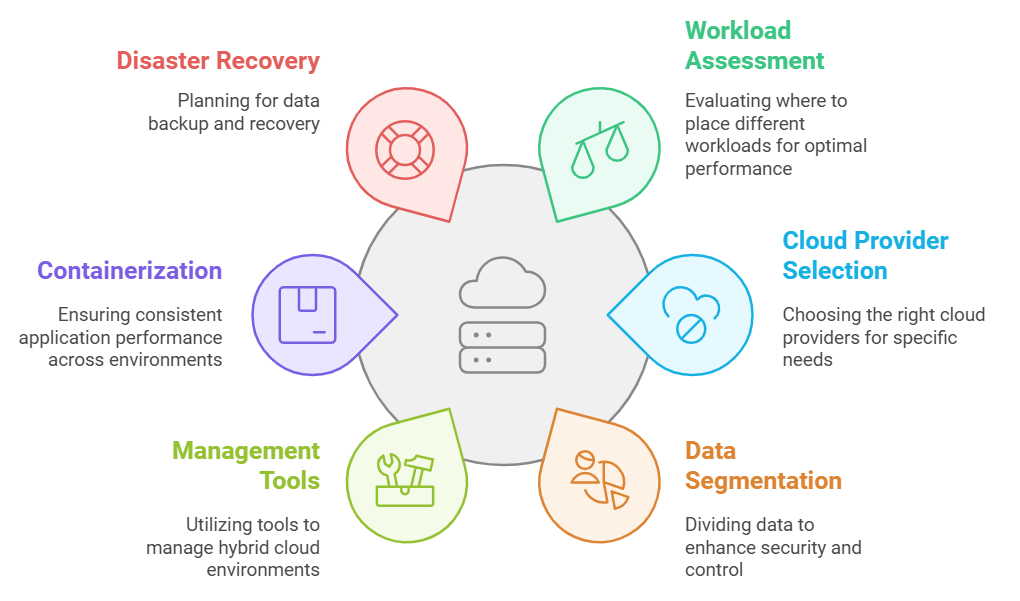
Integrating Disparate Systems
Disconnected systems are a hidden source of bottlenecks. When your CRM, ERP, and project management tools don’t communicate, employees spend time duplicating work, reconciling data, and chasing updates, a classic example of the friction cost mental model, where each handoff adds delays and errors.
Custom software solves this by:
- Creating seamless connections between platforms – Data flows automatically between systems, reducing manual transfers and inconsistencies.
- Eliminating redundant tasks – For example, sales updates no longer need to be manually entered into finance or operations systems.
- Providing a unified view of operations – Teams can see the full picture in real time, enabling faster decisions and proactive bottleneck management.
Consider a scenario where marketing, sales, and customer support each maintain separate databases. Integrating these systems has been shown in multiple case studies to boost operational efficiency by up to ~30%, reduce redundant data entry, and streamline reporting—helping cut duplicated effort and accelerate responses.
By breaking down these silos, custom software ensures that your departments aren’t working in isolation, and information flows smoothly from one team to another.
Real-Time Data & Reporting
Bottlenecks often appear because decisions are made on outdated or incomplete information. Waiting for reports or manually compiling data introduces delays and increases the risk of errors, a classic example of the information latency mental model, where the value of information decreases the longer it takes to reach decision-makers.
Custom software tackles this by:
- Providing live dashboards – Teams can monitor KPIs, approvals, and workflows in real time without waiting for end-of-day or weekly reports.
- Enabling proactive decision-making – Alerts and insights flag issues before they become bottlenecks, allowing teams to act immediately.
- Reducing report preparation time – Automated reporting frees employees from manual data compilation, cutting hours or even days from critical processes.
For instance, a sales manager tracking leads across multiple platforms might spend 5–7 hours weekly consolidating data. With real-time reporting, that time drops to minutes, enabling faster follow-ups and better pipeline management. By giving teams timely, actionable insights, custom software transforms bottlenecks from hidden slowdowns into opportunities for efficiency.
Next Steps
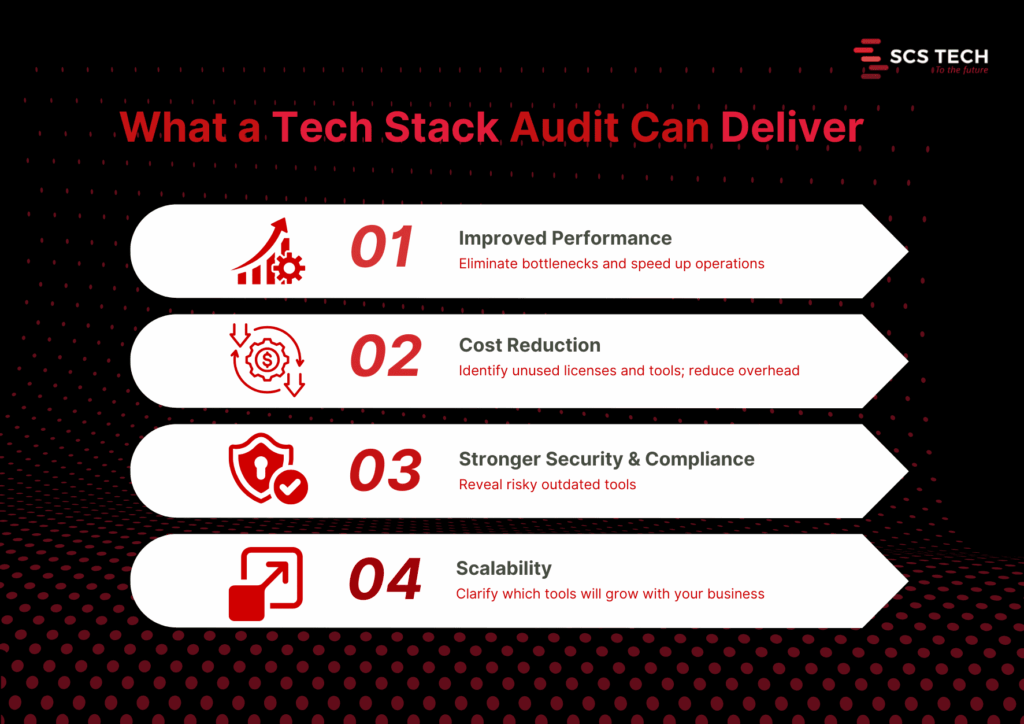
Custom software development has the power to remove bottlenecks, streamline workflows, and give your teams more time for high-value work. From operations and finance to HR and sales, the right solution makes processes faster, more reliable, and easier to manage.
At SCSTech, we specialize in designing and implementing custom software that addresses your unique operational challenges. Our experts work closely with you to identify pain points, create tailored solutions, and ensure smooth adoption across departments.
Contact SCSTech today to speak with our experts and discover how custom software can transform bottlenecks into seamless, high-efficiency workflows for your business.