Are you aware that ransomware attacks worldwide increased by 87% in February 2025? The sharp peak highlights the need for organizations to review their cybersecurity strategies. Standard solutions, as often one-size-fits-all, cannot specifically address the vulnerabilities of individual organizations and cannot match evolving cybercriminal methods.
In contrast, custom cybersecurity solutions are designed to address an organization’s requirements, yielding flexible defences bespoke to its infrastructure. When integrated with Zero Trust Architecture—built around ongoing verification and strict access control—such solutions create a comprehensive defence against increasingly advanced ransomware attacks.
This blog will examine how custom cybersecurity solutions and Zero Trust Architecture come together to create a strong, dynamic defence against the increasing ransomware threat.
Custom Cybersecurity Solutions – Targeted Defense Against Ransomware
Unlike one-size-fits-all generic security tools, customized solutions target unique vulnerabilities and provide adaptive defences suited to the organization’s threat environment. This particularity is crucial in ransomware combat since ransomware frequently attacks specific system weaknesses.
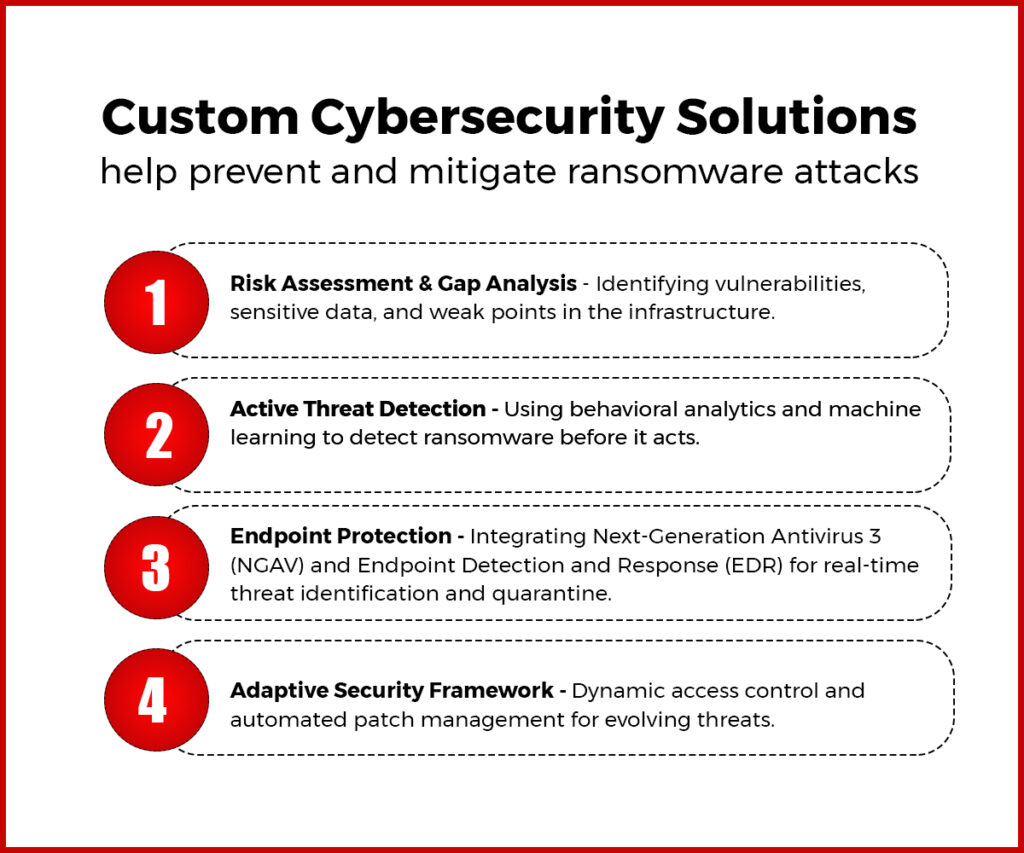
Key Features of Custom Cybersecurity Solutions That Fight Ransomware
1. Risk Assessment and Gap Analysis
Custom cybersecurity solutions start with thoroughly analysing an organization’s security position. This entails:
- Asset Identification: Organizations must identify key data and systems that need increased security. These are sensitive customer data, intellectual property, and business data that, if breached, would have devastating effects.
- Vulnerability Analysis: By doing this analysis, organizations determine vulnerabilities like old software, misconfiguration, or exposed endpoints that ransomware can target. This ensures that security solutions are designed to counter specific risks instead of general protection.
The result of such intensive evaluation guides the creation of focused security measures that are more efficacious for countering ransomware attacks.
2. Active Threat Detection
Custom-made security solutions incorporate the best detection features designed to detect ransomware behaviour before its ability to act. The integral parts are:
- Behavioral Analytics: These platforms track user and system activity for signs of anomalies suggesting ransomware attempts. For instance, unexpected peaks in file encryption activity or unusual access patterns may indicate a threat.
- Machine Learning Models: Using machine learning algorithms, organizations can forecast patterns of attacks using historical data and developing trends. These models learn continuously from fresh data, and their capacity to identify threats improves with time.
This proactive strategy allows organizations to recognize and break up ransomware attacks at the initial phases of the attack cycle, significantly reducing the likelihood of data loss or business disruption.
3. Endpoint Protection
Endpoints—laptops, desktops, and servers—are common entry points for ransomware attacks. Customized solutions utilize aggressive endpoint protection that involves:
- Next-Generation Antivirus (NGAV): Compared to traditional signature-based detection-based antivirus solutions, NGAV applies behaviour-based detection mechanisms for identifying known and unknown threats. This is necessary to identify new ransomware strains that have not received signatures.
- Endpoint Detection and Response (EDR): EDR solutions scan endpoints in real-time for any suspicious activity and can quarantine a compromised endpoint automatically from the network. Containing this way prevents ransomware from spreading throughout the networks of an organization.
By putting endpoint security first, bespoke cybersecurity solutions protect against ransomware attacks by making possible entry points secure.
4. Adaptive Security Framework
Custom solutions are created to adapt to developing threats to maintain ongoing protection through:
- Dynamic Access Controls: These controls modify users’ permissions according to up-to-the-minute risk evaluations. For instance, if a user is exhibiting unusual behaviour—such as looking at sensitive files outside regular working hours—the system can restrict their access temporarily until further verification is done.
- Automated Patch Management: One must stay current with updates to address vulnerabilities that ransomware can exploit. Automated patch management maintains all systems up to the latest security patches without manual intervention.
This dynamic system enables companies to defend themselves against changing ransomware strategies.
Zero Trust Architecture (ZTA) – A Key Strategy Against Ransomware
The Zero Trust Architecture cybersecurity functions on the “never trust, always verify” paradigm. It removes implicit network trust by insisting on ongoing authentication and rigorous access controls on all users, devices, and applications. This makes it highly effective against ransomware because of its focus on reducing trust and verifying all requests to access.
Key Features of ZTA That Counteract Ransomware
1. Least Privilege Access
Ransomware usually takes advantage of over permissions to propagate within networks. ZTA implements least privilege policies through:
- Limiting User Access: Users are given access only to resources required for their functions. This reduces the impact if an account is compromised.
- Dynamic Permission Adjustments: Permissions are adjustable by contextual properties like location or device health. For instance, if a user is trying to view sensitive information from an unknown device or location, their access can be denied until additional verification is done.
This tenet significantly lessens the chances of ransomware spreading within networks.
2. Micro-Segmentation
ZTA segments networks into smaller zones or segments; each segment must be authenticated separately. Micro-segmentation restricts the spread of ransomware attacks by:
- Isolating Infected Systems: When a system is infected with ransomware, micro-segmentation isolates the system from other areas of the network, eliminating lateral movement and further infection.
- Controlled Segmentation Between Segments: Each segment may have its access controls and monitoring mechanisms installed, enabling more detailed security controls specific to types of data or operations.
By using micro-segmentation, organizations can considerably lower the risk of ransomware attacks.
3. Continuous Verification
In contrast to legacy models that authenticate users one time upon login, ZTA demands continuous verification throughout a session.
- Real-Time Authentication Verifications: Ongoing checks ensure that stolen credentials cannot be utilized in the long term. If suspicious activity is noted within a user session—e.g., access to unexpected resources—the system may request re-authentication or even deny access.
- Immediate Access Denial: If a device or user acts suspiciously with signs of a possible ransomware attack (e.g., unexpected file changes), ZTA policies can deny real-time access to stop the damage.
This ongoing validation process strengthens security by ensuring only valid users retain access during their interactions with the network.
4. Granular Visibility
ZTA delivers fine-grained visibility into network activity via ongoing monitoring:
- Early Ransomware Attack Detection: Through monitoring for off-the-book data transfers or unusual file access behaviour, organizations can recognize early indications of ransomware attacks before they become full-fledged incidents.
- Real-Time Alerts: The design sends real-time alerts for anomalous activity so that security teams can react promptly to suspected threats and contain threats before they cause critical harm.
This level of visibility is essential to ensuring an effective defence against advanced ransomware techniques.
Why Custom Cybersecurity Solutions and Zero Trust Architecture Are Best Against Ransomware?
1. Holistic Security Coverage
Custom cybersecurity solutions target organization-specific threats by applying defences to individual vulnerabilities. Zero Trust Architecture delivers generic security guidelines for all users, devices, and applications. They offer complete protection against targeted attacks and more general ransomware campaigns.
2. Proactive Threat Mitigation
Custom solutions identify threats early via sophisticated analytics and machine learning algorithms. ZTA blocks unauthorized access completely via least privilege policies and ongoing verification. This two-layered method reduces opportunities for ransomware to enter networks or run successfully.
3. Minimized Attack Surface
Micro-segmentation in ZTA eliminates lateral movement opportunities across networks, and endpoint protection in bespoke solutions secures shared entry points against exploitation. Together, they cut the general attack surface for ransomware perpetrators drastically.
4. Scalability and Flexibility
Both models fit in perfectly with organizational expansion and evolving threat horizons:
- Bespoke solutions change through dynamic security controls such as adaptive access controls.
- ZTA scales comfortably across new users/devices while it enforces rigid verification processes.
In tandem, they deliver strong defences regardless of organizational size or sophistication.
Conclusion
Ransomware threats are a serious concern as they target weaknesses in security systems to demand ransom for data recovery. To defend against these threats, organizations need a strategy that combines specific protection with overall security measures. Custom cybersecurity solutions from SCS Tech provide customised defenses that address these unique risks, using proactive detection and flexible security structures.
At the same time, zero trust architecture improves security by requiring strict verification at every step. This reduces trust within the network and limits the areas that can be attacked through micro-segmentation and continuous authentication. When used together, these strategies offer a powerful defense against ransomware, helping protect organizations from threats and unauthorized access.
